With Kherson firmly back in Ukrainian hands, officials now have the grueling task of restoring order to the port city after nearly nine months of Russian military occupation.
An undertaking that, in less than a week of liberation, has involved the investigation of war crimes, dismantling of mines and booby traps, and for the Security Services of Ukraine (SBU), searches for local collaborators and foreign agents of Russia’s security and intelligence services which could still be lurking in the area.
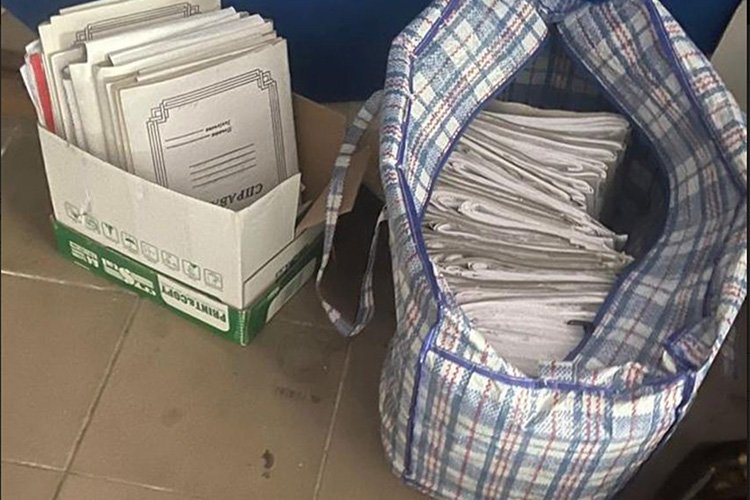
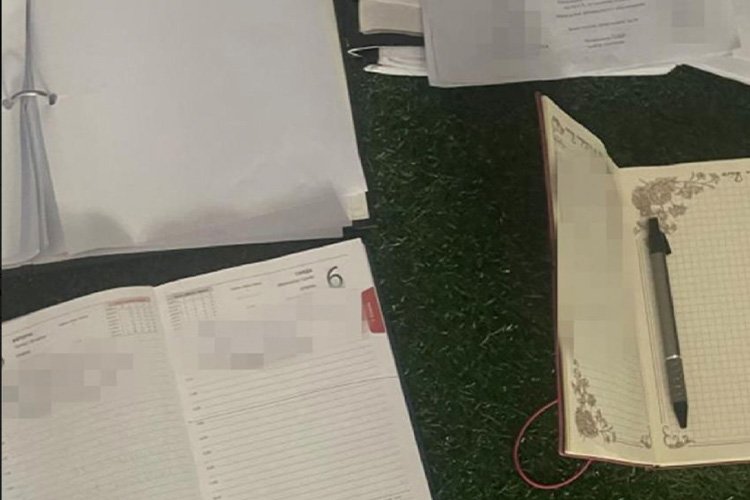
The hunt for the enemy within was recently made a little easier after SBU officers discovered a trove of classified documents left behind by Russia’s Federal Security Service, FSB, during its hasty retreat from Kherson.
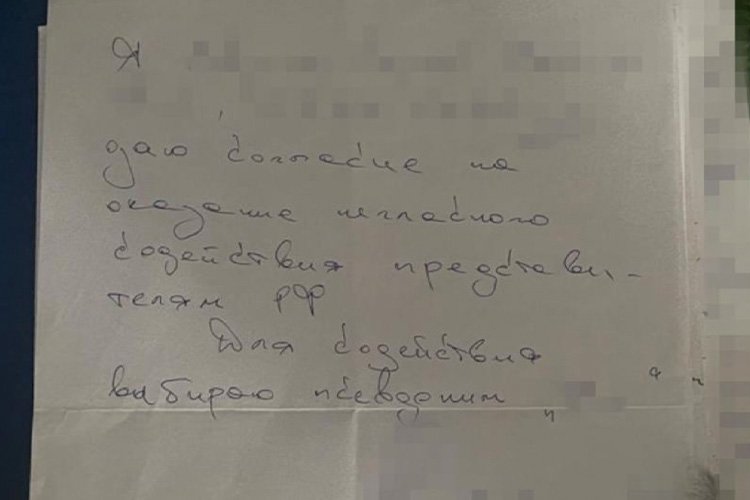
SBU says amongst the boxes of abandoned documents is detailed information on agents who collaborated with Russia during Kherson’s occupation, including handwritten notes detailing “obligations” to provide confidential information to FSB.
The Debrief was first made aware of the discovery by a source within the Intelligence Community who was familiar with the incident and later confirmed by SBU in a posting on Telegram.
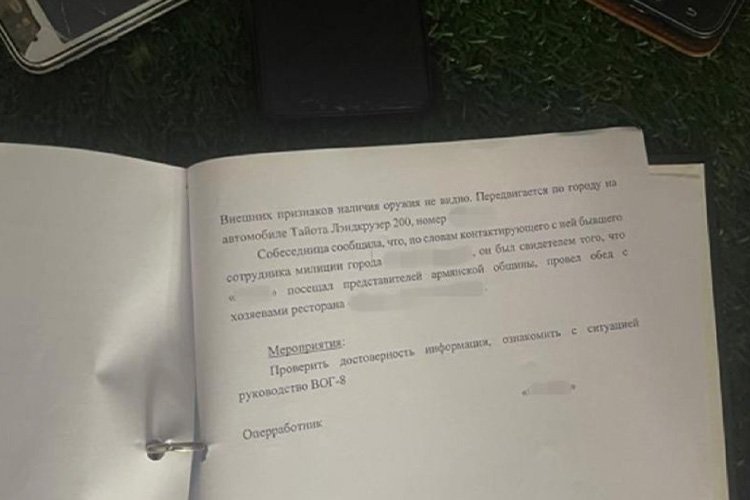
According to SBU, documents detail the system FSB was using for local collaborators to provide “tips” to Russian authorities on pro-Ukrainian citizens, particularly the activities of local resistance groups in the Kherson region.
Among the discarded paperwork were personal files of Russian agents, reports on FSB activities, and protocols for searching local residences were also reportedly discovered.
“Documented facts of abduction and torture of the victims, as well as the looting of their homes under the guise of conducting ‘searches’ were also revealed,” according to SBU officials.
According to SBU, the trove of documents reportedly found in a Kherson area garage originated from an FSB “temporary operational group” known as “VOG-8.”
Without elaborating, a source familiar with the discovery said it’s possible, but unlikely, that the documents are misinformation deliberately left behind by FSB to tie up SBU resources.
“They will be carefully investigated, but there are reasons to believe they are authentic,” said the individual under a condition of anonymity as they were not authorized to speak on the record.
In a public statement, SBU said, “the seized materials have been sent for examination for further operational actions to expose Russian intelligence networks.”
Before the discovery of the classified FSB documents, SBU announced that it would concentrate on stabilizing measures in the de-occupied territories of Kherson Oblast, including hunting down local collaborators or foreign agents that had been purposefully left behind as part of a Russian fifth column.
On November 14, SBU officers arrested a Russian soldier dressed in civilian clothes in the Kherson region. The soldier reportedly confessed to being with Russia’s 69th Covering Brigade, tasked with clandestine operations, including collecting intelligence, carrying out sabotage, and adjusting Russian long-range fires on Ukrainian military targets.
The following day, SBU also arrested a Russian citizen living in one of the border villages of the Chernihiv region. SBU said the man, who had lived in Ukraine for several years, was an FSB spy helping provide Russia with intelligence on Ukrainian troop movements near the northern border.
Ukraine has also set up several hotlines, emails, and social media chatbots where individuals can anonymously report information on suspected Russian collaborators or foreign agents.
Persons suspected of aiding Russia in its ongoing invasion could face criminal charges under Article 111-2.1, “Aiding the Aggressor State,” a crime punishable by up to 12 years in prison.
“We understand that the enemy could have intentionally left its agents in the de-occupied territory to perform certain actions. Our task is to identify them,” said SBU’s acting director, Vasyl Maliuk.
“SSU has intelligence on traitors and collaborators who defected to the enemy – we are verifying this information on the spot. All those who betrayed Ukraine for the sake of ‘Russkiy mir’* will receive well-deserved punishment.”
* “Russkiy Mir,” translated into English, means “Russian World.” The phrase represents a political ideology, often touted by Russian President Vladimir Putin, that nations with a shared Russian history, such as former Soviet or Russian-speaking nations, should be part of one unified Russian state.
Tim McMillan is a retired law enforcement executive, investigative reporter and co-founder of The Debrief. His writing typically focuses on defense, national security, and the Intelligence Community. You can follow Tim on Twitter: @LtTimMcMillan. Tim can be reached by email: tim@thedebrief.org or through encrypted email: LtTimMcMillan@protonmail.com

